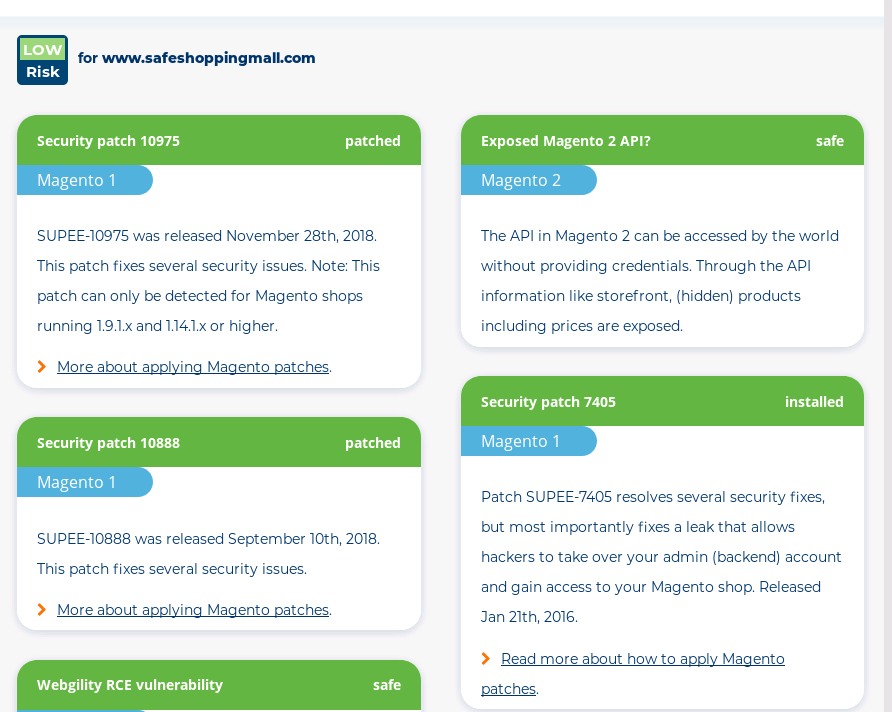
In details, we check current state, verify already applied patches, local overrides and install the following security patches for Magento 1.x:
Patches for CVE-2022-24086, CVE-2021-32759, CVE-2021-32758, CVE-2021-21427, CVE-2021-21426, CVE-2020-26295, CVE-2020-26285, CVE 2020-26252, CVE-2020-15244, APSB20-47, SUPEE-11346, SUPEE-11314, SUPEE-11295, SUPEE-11219, SUPEE-11155, SUPEE-11086, SUPEE-10975, SUPEE-10888, SUPEE-10752, SUPEE-10570v2, SUPEE-10415, SUPEE-10266 (or SUPEE-10497 for 1.9.1.1 version), SUPEE-9767 v2, SUPEE-9652, SUPEE-8788, SUPEE-7405v1.1, SUPEE-7405, SUPEE-6788, SUPEE-6482, SUPEE-6285, SUPEE-5994, SUPEE-5344, SUPEE-3941, SUPEE-3762, SUPEE-2725/1049 and APPSEC-212, compatibility patches SUPEE-11085, SUPEE-10336, SUPEE-8167, SUPEE-7616, SUPEE-6237, SUPEE-4291/4334 and SUPEE-1868. Additionally, we patch known RCE vulnerabilities in the following third-party extensions: EM Ajaxproducts RCE vulnerability, Cart2Quote RCE vulnerability, MD Quickview RCE vulnerability, EM Quickshop RCE vulnerability, Amfeed vulnerability and fix any issues should they happen after patch installation.
Magento security patch installation process is usually completed within eight hours:
- you submit the request form and initiate payment
- we connect to your servers to verify checksum of Magento core files and get file-by-file state of all already applied patches, local overrides, extensions
- we backup all files to be patched
- we disable Magento compiler (if needed)
- we apply all needed security patches one by one solving any possible issues that may arise
- we patch all local overrides that were skipped during patch installation
- we flush PHP opcode cache (if needed)
- we apply fixes for known issues that may arise after patch installation
- we verify integrity of store home page, catalog pages, checkout process
- we notify you about the process completion
See sample transcript of patching by our tech in action here.
Moneyback guarantee: backed by PayPal.
PayPal is always on your side.